Session 1
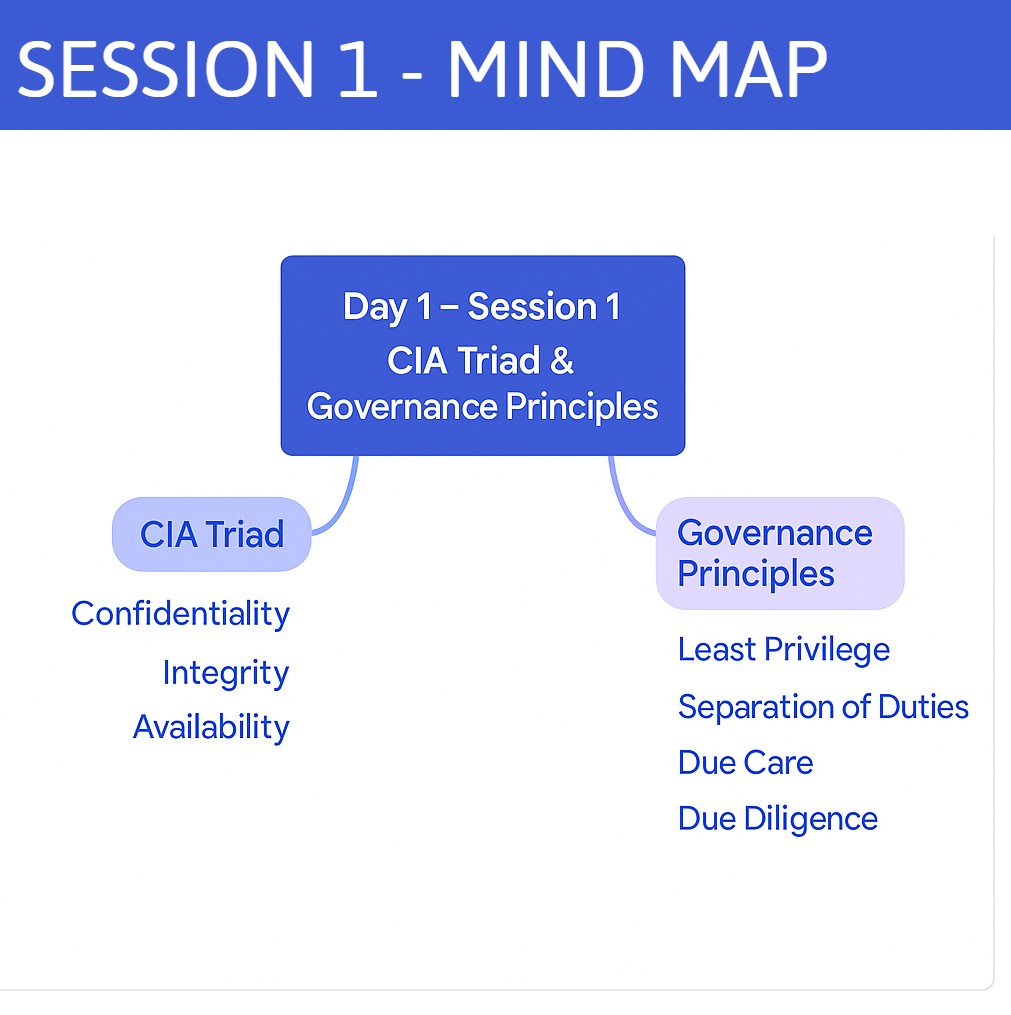
- Quick refresher on the CIA triad (confidentiality, integrity, availability)
- Security governance fundamentals: roles, organizational structure, and frameworks
- Key compliance standards overview (e.g. ISO 27001, NIST CSF)
- Distinctions between policies, standards, procedures, and guidelines
Good morning, everyone. Today we kick off our CISSP journey with Domain 1: Security & Risk Management. Over the next 5–10 minutes, I want you to understand exactly what we’ll cover and why it matters:
- CIA Triad Refresher
We’ll revisit Confidentiality, Integrity, and Availability—the bedrock of any security program. You’ll hear real‐world examples of how each pillar protects an organization’s data and operations.
- Security Governance Fundamentals
You’ll learn the roles and responsibilities of key stakeholders—from executives setting strategy, to security architects designing controls, to auditors verifying compliance. We’ll map out a simple governance framework so you can see how policy flows from boardroom to break room.
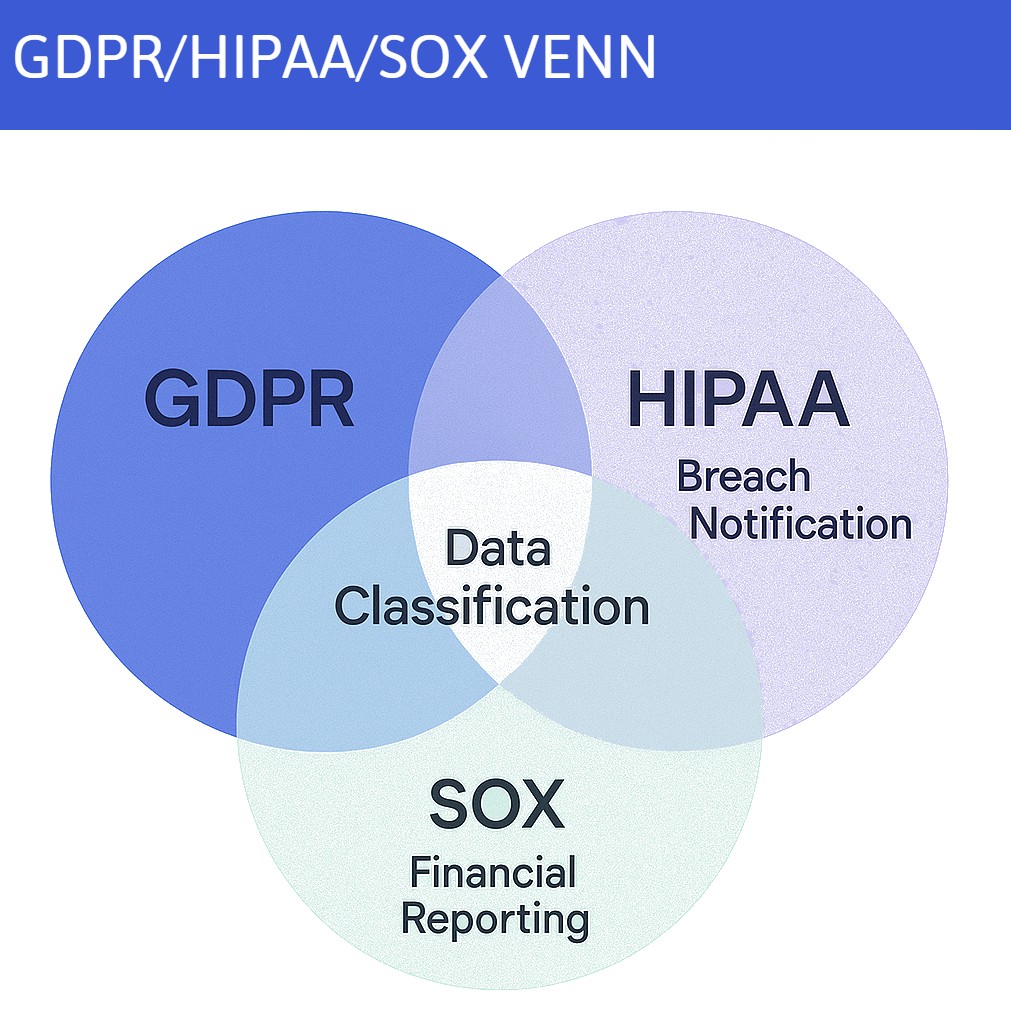
- Compliance Standards Overview
We'll touch on ISO 27001, the NIST Cybersecurity Framework, and other regulations. I’ll highlight the common threads—risk assessment, continuous improvement—and point out where they differ.
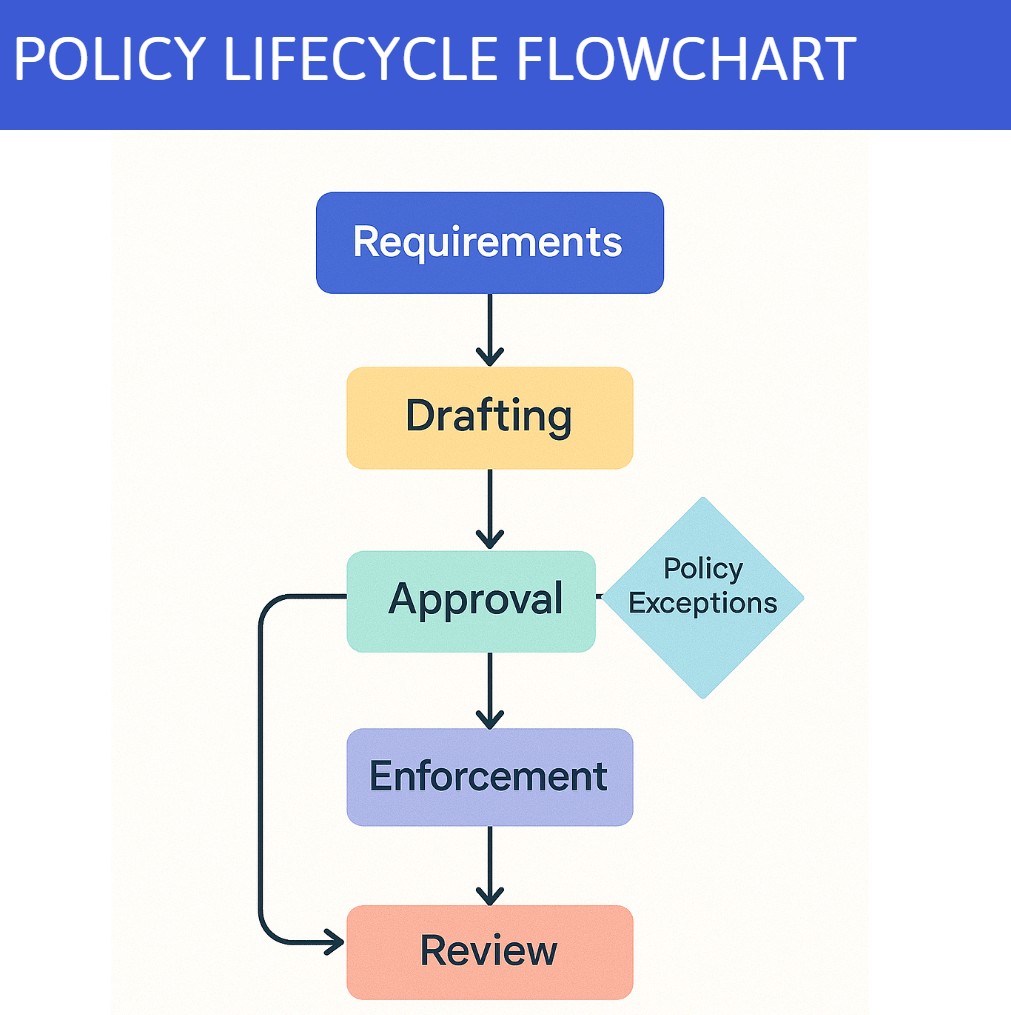
- Policies vs. Standards vs. Procedures vs. Guidelines
Finally, we’ll clarify the hierarchy: why a policy tells you what you must do, a standard tells you how to measure it, a procedure shows step-by-step execution, and guidelines offer best practice tips. By the end of this preview, you’ll know which document to reach for when you need to write or review security documentation.
Take these objectives to heart—this domain underpins the rest of the CISSP. Once we finish, you’ll be primed to dive deeper into the legal, ethical, and procedural controls that keep organizations safe.”
Concepts to Place
Got It
Still Working on It